molitar wrote:Thanks intika! Good work. BTW all if you are using PAE Patcher to patch your kernel than rename the ntkrnlpx.exe for the version check. Once I had used resource hacker to edit the original exe file it worked good once I caught that rename.
Use last version instead

it's better
molitar wrote:
May I ask what program you use to patch the kernel? I been using a patcher that creates a second kernel and the boot loader points to that kernel but than that means it never gets patched. Sounds like you have a better patch method that points to the new patch kernel and than this application of yours lets you know there is an update to patch the new file. I would like a copy of that patcher so I can update my kernel when it's updated.
Thanks.
I forgot to mention the one I am using does not currently show the version I am using. Same with the tcp/ip patcher that I use to crack the 10 concurrent connection limit so the app will not work for me at this time unless I can get pointed to or get a copy of the patcher you use for these two limitations.
4GB limit patch
10 concurrent connection patch.
Thanks
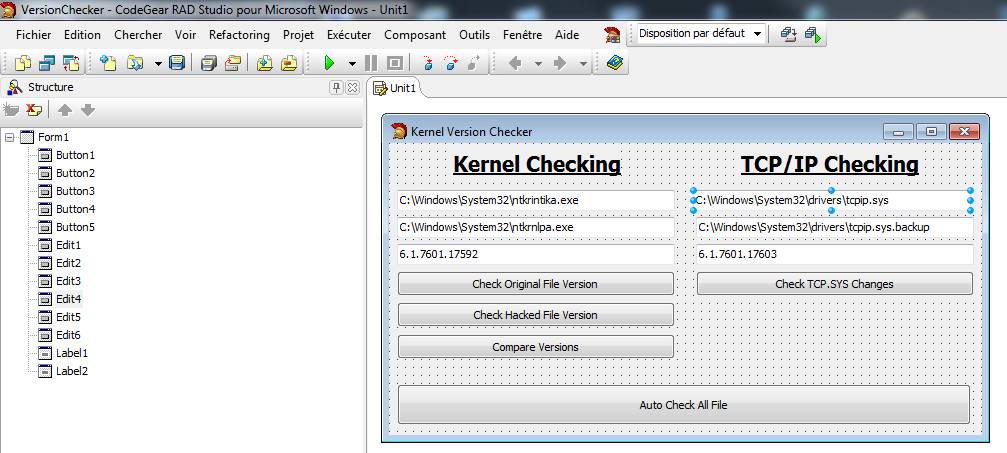
For TCPIP Here is the patch that i use ...
For kernel file i patch it manually, i could create a patcher but don't want to play with that because i have to be sure at 200% it's why i patch it manually... it's very easy... it work the same way as you patcher, i created a boot entry pointing to my patched kernel and set it as defaut, then the computer boot directly to the patched file...
in the boot menu you can change that value with "easybcd"...
To patch i use "makecert.exe" and "signtool.exe" + "HexCmp"
as you understand, original file "C:\Windows\System32\ntkrnlpa.exe" is never touched, for a simple purpose, it's that file that get updated by windows every time, then you have to keep it untouched and boot with an other file. (the "ntkrnlpa.exe" is there and get updated but it's not used as you don't use it to boot)
Here is the steps i do to patch
1. Copy ntkrnlpa.exe to ntkrnlpatched.exe (rename it as you want, don't forget to point the good file in your BCD)
2. Open ntkrnlpatched.exe to edit in hex with HexCmp
3. Look for 7C118B45FC85C0740A and 7C108B45FC85C07409
Original : 7C 11 8B 45 FC 85 C0 74 0A
Patched : 7C 11 B8 00 00 02 00 90 90
Original : 7C 10 8B 45 FC 85 C0 74 09
Patched : 7C 11 B8 00 00 02 00 90 90
4. Replace with patched value and save
5. Create certificate with the following command (you have to do it once, not needed for next patch)
makecert -r -ss my -n "CN=Microsoft Windows"
6. Sign the new ntkrnlpatched.exe with the following command
signtool sign -s my -n "Microsoft Windows" -a ntkrnlpatched.exe
That's it

I provided you the how to and patching tools here

Note : if you don't know how to create boot entry pointing to patched file, just use easybcd to copy current one, and then edit it to make it load to the patched kernel
Download TCP IP Patcher
http://aliappz8.free.fr/tmp/TCP.IP.Univ ... .Patch.rar
Download Kernel Patcher
http://aliappz8.free.fr/tmp/Kernel.Patcher.Manual.rar
Cheers